CLOUD SERVICES FOR SPAMMERS
A security update from WordFence
CompanyV has been a long time customer of WordFence for WordPress.
The following entry was posted on Wordfence.com in General Security, WordPress Security on February 23, 2017 by Mark Maunder
Cloudflare has experienced a data leak over a 5 month period that mixed sensitive data between websites and visitors. A visitor to one website using Cloudflare may have seen data from another website using Cloudflare that was being sent to a completely different site visitor.
Some of the leaked data has been indexed by search engines who have been working over the past few days to try and remove the data from their caches.
In this post I am going to explain in simple terms, what occurred and what you need to do about it.
If you are a WordPress user and simply want to know how to secure your site, you can skip to the What Should I Do section below. I have included some information for non-WordPress site owners in that section too.
Click here for the full post on Wordfence: Cloudflare Data Leak: How to Secure Your Site
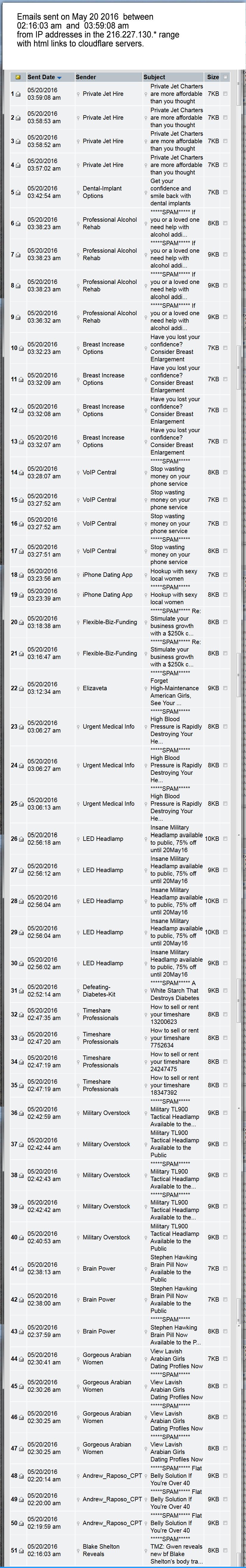
Cloudflare hosting obsfucates spam hosts
May 20, 2016 update
One inbox has 51 emails from a single mail server range:
NetRange: 216.227.128.0 - 216.227.191.255
CIDR: 216.227.128.0/18
NetName: FDCSERVERS
NetHandle: NET-216-227-128-0-1
Parent: NET216 (NET-216-0-0-0-0)
NetType: Direct Allocation
OriginAS: AS174, AS30058, AS6461
Organization: FDCservers.net (FDCSE)
RegDate: 2013-05-01
Updated: 2015-11-09
Ref: https://whois.arin.net/rest/net/NET-216-227-128-0-1
We can block the sending mail servers but the spammers will be sending mail tomorrow from new cheap hosted mail accounts.
ALL LINKS LEAD TO CLOUDFLARE
The html links are all to cloudflare IP addresses:
NetRange: 104.16.0.0 - 104.31.255.255
CIDR: 104.16.0.0/12
NetName: CLOUDFLARENET
NetHandle: NET-104-16-0-0-1
Parent: NET104 (NET-104-0-0-0-0)
NetType: Direct Assignment
OriginAS: AS13335
Organization: CloudFlare, Inc. (CLOUD14)
RegDate: 2014-03-28
Updated: 2015-10-01
Comment: https://www.cloudflare.com
Ref: https://whois.arin.net/rest/net/NET-104-16-0-0-1
From Honey Pot development to the dark side?
In 2004, Matthew Prince and Lee Holloway set out to answer the basic question: “Where does email spam come from?” The two of them built a system that allowed anyone with a website to track how spammers harvested email addresses. Project Honey Pot was born.
Project Honey Pot quietly grew over the years. Lee’s flexible architecture adapted to track more of the threats that web administrators faced. Thousands of websites, from more than 185 countries, signed up to participate in the project. While users loved Project Honey Pot’s ability to track online malicious behavior, they had one repeated request: don’t just track the bad guys, stop them.
They go on to say…
The intention was to clean up the internet…
In other words
It seems spam links are fine.
If this was just some tech wiz start up I would not be as taken aback – but the background of the developers seems to indicate that if you study SPAM enough – you can fight it – or sell services to do it better.
One step forward two steps back
The rush to cloud services has created a time consuming wasteful and dangerous playing field.
Are those few moments of latency reduction worth the time it takes to clear the spam from your inbox?
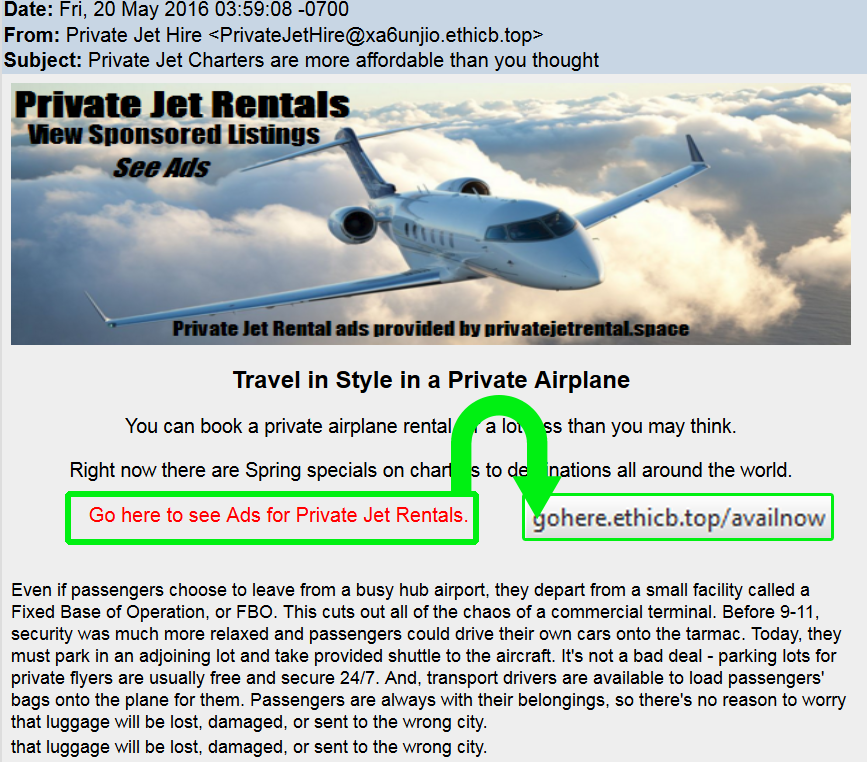
Obfuscated URL
Definition – What does Obfuscated URL mean?
An obfuscated URL is a web address that has been obscured or concealed and has been made to imitate the original URL of a legitimate website. It is done to make users access a spoof website rather than the intended destination.Obfuscated URLs are one of the many phishing attacks that can fool Internet users. The spoof site is often an identical clone of the original one in order to fool users into divulging login and other personal information.
An obfuscated URL is also called a hyperlink trick.
Techopedia explains Obfuscated URL
Attackers usually use a common misspelling technique where they misspell a domain name to trick users into visiting. These obfuscated URLs can be a cause of malware entering a user’s computer system.
URL obfuscation is used together with spamming, redirecting users using a misleading URL that leads to a malicious site. URLs are strings of text that identify web resources such as websites or any kind of Internet server, so an obfuscated URL shows up as a meaningless query string to users.
This hides the real address of the linked site when the user hovers over the link. URL obfuscation is not always used for phishing or cross-site scripting, but it is also used by legitimate websites to hide the true URLs of certain pages so that they cannot be accessed directly by the users or allow certain procedures to be bypassed. It is also used as an anti-hacking procedure. This is termed as security through obscurity.
ref: https://www.techopedia.com/definition/4033/obfuscated-url
Faster more reliable spam links
Sorry but I do not understand how this is “cleaning up the internet”!
2016 has brought an onslaught of new spam from globally distributed IP ranges – the mail host are certainly responsible for allowing the spam through their networks and should be held accountable.
The recent most disturbing trend I see is huge batches of emails from multiple mail servers from multiple countries – all with the same html basic template and layout all linking to different websites.
What ties them together?
It’s all about the destination!
The links in an abundance of these spam blasts resolve to Cloudflare ranges.
Fast, Global Content Delivery Network for spam delivery!

On their abuse page they say:
We accept the following kinds of reports:
- Copyright infringement & DMCA violations
- Trademark infringement
- Child pornography
- Phishing & malware
- Violent threats